Learn how to define and measure operational efficiency in security with key metrics, benchmarks, and sensor strategies tailored for Southeast Asia agencies.

Defining operational efficiency in security: insights & best practices

TL;DR:
- Operational efficiency in security focuses on maximizing threat detection, investigation, and response with minimal resources.
- Key metrics include MTTD under 1 hour, MTTR under 4 hours, false positive rates below 30%, and automation coverage of 50-70%.
- Combining human judgment with automation and regional compliance ensures resilient and region-specific security operations.
Operational efficiency in security is not simply about deploying the latest sensors or automating every alert. Most agencies and large organizations across Southeast Asia invest heavily in technology yet still struggle with slow response times, bloated alert queues, and compliance gaps. The real definition is sharper: maximizing security outputs while minimizing resource inputs across detection, investigation, and response. This article walks you through the foundational metrics, proven methodologies, and regional context you need to move from confusion to confident, measurable operational clarity.
Table of Contents
- Clarifying operational efficiency in security
- Key metrics and global/regional benchmarks
- Methodologies and advanced sensor strategies
- Navigating edge cases, compliance, and physical-cyber convergence
- Why efficiency alone can mislead in security operations
- Accelerate your agency's efficiency with BeyondSensor
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Efficiency is measurable | Operational efficiency in security is defined by outputs versus inputs, not just technology investment. |
| Benchmarks drive improvement | MTTD, MTTR, automation coverage, and false positive rates are core, global metrics for evaluating security operations. |
| Balance automation with oversight | Automated processes enhance efficiency but require routine human audits to avoid alert fatigue and missed threats. |
| ASEAN context matters | Southeast Asia’s regulatory environment and maturity necessitate customized frameworks and compliance strategies. |
| Beyond numbers: resilience counts | Cultivating adaptive, resilient security cultures is essential for sustainable operational excellence. |
Clarifying operational efficiency in security
Many security leaders conflate efficiency with sophistication. A facility running six different sensor platforms is not automatically efficient. Efficiency means your team detects more threats, investigates faster, and responds decisively, all without burning through budget or personnel. Defining SecOps efficiency starts with understanding what you are actually optimizing.
At its core, operational efficiency maximizes detection, investigation, and response through optimized resource inputs. That means every dollar spent and every analyst hour logged should produce a measurable security outcome. It is not about speed alone. A team that closes incidents in 10 minutes but misclassifies 40% of them is not efficient. It is busy.
Here are the foundational pillars of security operational efficiency:
- Threat detection: Identifying genuine threats with high accuracy and low false positive rates
- Investigation: Correlating signals quickly to build actionable incident context
- Response: Executing containment and remediation with minimal delay and resource waste
- Resource minimization: Achieving the above without overstaffing or over-engineering
Two common pitfalls undermine efficiency in practice. First, over-automation. Teams that automate everything, including nuanced behavioral anomalies, often create alert fatigue from high false positives, where analysts stop trusting the system and start ignoring alerts. Second, inadequate metrics. Without baselines, you cannot tell whether your operations are improving or degrading.
"Efficiency is not excellence. Short-term process optimization is not the same as long-term cultural resilience." This distinction matters because agencies that chase efficiency scores alone often sacrifice adaptability when threat landscapes shift.
The goal is a balanced operation: automated where repetitive, human-led where contextual, and always grounded in measurable outcomes.
Key metrics and global/regional benchmarks
With efficiency defined, the next step is measuring it precisely. The metrics that matter most in security operations center (SOC) environments are well established globally, but their targets vary by maturity and region.
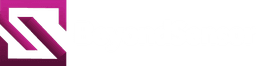
The five core metrics every security team should track are:
- Mean Time to Detect (MTTD): How quickly you identify a threat after it occurs
- Mean Time to Respond (MTTR): How fast you contain and remediate after detection
- Dwell time: How long a threat persists undetected in your environment
- False positive rate: The percentage of alerts that turn out to be non-threats
- Automation coverage: The share of repetitive tasks handled without human intervention
Elite SOC benchmarks set MTTD under 1 hour, MTTR under 4 hours for critical incidents, false positive rates below 20 to 30%, dwell time under 21 days, and automation coverage between 50 and 70%. These are not aspirational numbers. They are the operating standard for high-performing teams.
| Metric | Global elite target | ASEAN developing baseline |
|---|---|---|
| MTTD | Under 1 hour | Under 24 hours |
| MTTR | Under 4 hours | Under 12 hours |
| Dwell time | Under 21 days | Under 60 days |
| False positive rate | Below 20% | Below 40% |
| Automation coverage | 50 to 70% | 30 to 50% |
For government agencies in Southeast Asia, ASEAN efficiency benchmarks are shaped by regulatory alignment, digital maturity, and governance priorities rather than pure technical capability. Agencies tracking government agency benchmarks often use composite scores across NIST Cybersecurity Framework (CSF) functions. FISMA metrics via NIST CSF guide critical infrastructure operators toward foundational practices through CISA Cybersecurity Performance Goals (CPGs).
How do you act on these metrics? Follow this sequence:
- Establish your current baseline across all five metrics using historical incident data
- Identify which metric shows the largest gap versus the regional or global target
- Prioritize one metric for a 90-day improvement sprint before moving to the next
- Validate improvements against real incident outcomes, not just dashboard scores
- Review mastering security compliance and physical security standards to ensure metric improvements align with regulatory requirements
Metrics without context are just numbers. Tie every measurement to a specific operational outcome to make them genuinely useful.
Methodologies and advanced sensor strategies
Having identified the metrics, the next question is what methodologies actually move them. Three approaches dominate modern security operations: automation, behavioral analytics, and advanced sensor deployment.
| Methodology | Primary benefit | Key risk | Best use case |
|---|---|---|---|
| Automation (SIEM, SOAR, AI) | Reduces repetitive workload | Alert fatigue, missed nuance | High-volume, rule-based detection |
| Behavioral analytics | Detects anomalous patterns | Requires quality baseline data | Insider threats, lateral movement |
| Advanced sensor deployment | Increases physical coverage and accuracy | Integration complexity | Perimeter, critical infrastructure |
Automation of repetitive tasks through SIEM, SOAR, and AI platforms reduces analyst workload on low-value alerts. Behavioral analytics layers on top to catch what rules miss. Advanced sensor solutions, particularly in physical security, extend detection coverage to areas that purely digital tools cannot reach.
![]()
For agencies in ASEAN, sensor-based security advantages are especially relevant given the region's mix of dense urban infrastructure and remote critical assets. Sensors provide persistent, high-accuracy coverage that scales without proportionally scaling headcount.
Practical steps for integrating sensor technology while maintaining regional compliance:
- Map sensor placement against your highest-risk zones and existing detection gaps
- Define data retention and access policies aligned with local privacy regulations before deployment
- Integrate sensor feeds into your SIEM or SOAR platform to unify physical and cyber signals
- Establish nuisance alarm rate (NAR) targets alongside false positive rate targets for physical sensors
- Review tailored security approaches to avoid generic deployments that underperform in your specific environment
- Use sensor compliance tips to keep deployments audit-ready
Continuous improvement is the final layer. The SecOps prescriptive rubric from frameworks like NIST CSF provides structured baselines for each operational function, making it easier to identify where your process matures and where it stalls.
Pro Tip: Balance automation coverage with nuanced human oversight. A 60% automation rate means nothing if the remaining 40% of human-reviewed alerts are misclassified due to analyst burnout. Quality of review matters as much as volume of automation.
Navigating edge cases, compliance, and physical-cyber convergence
Beyond core metrics and strategies, real-world operations face complex edge cases and compliance demands that no dashboard fully captures.
The most common edge cases in sensor-powered security operations include:
- False positives at scale: High sensor density generates more alerts, amplifying false positive volume even at low individual rates
- Alert fatigue: Over-automation risks missing nuanced threats when analysts disengage from a flood of low-quality alerts
- Physical-cyber signal volume: Converged operations must reconcile physical sensor data with cyber event logs without creating blind spots in either domain
- Regulatory misalignment: Compliance requirements across Singapore, Malaysia, the Philippines, and upcoming markets vary enough to create gaps in unified security programs
Strategy mediates investments in Southeast Asia, explaining 68% of variance in security outcomes, which means regulatory context is not a footnote. It is a primary driver of what works and what does not.
A practical compliance checklist for ASEAN agencies:
- Align data handling and incident reporting with country-specific regulations (PDPA, CSA guidelines, NPC frameworks)
- Document sensor deployment rationale and coverage maps for audit purposes
- Conduct quarterly reviews of false positive rates and automation thresholds
- Maintain a physical-cyber convergence log that tracks how sensor events correlate with digital incidents
- Reference the step-by-step compliance guide for structured audit preparation
- Review virtual guard tour edge cases to understand how AI-assisted patrol handles ambiguous scenarios
Physical and cyber metrics serve different masters. Cyber metrics prioritize speed. Physical sensors prioritize accuracy and low nuisance alarm rates. Convergence demands that you set separate baselines for each and then create a unified escalation protocol that respects both. End user perspectives often reveal where these protocols break down in practice.
Pro Tip: Use tailored CPG-like baselines and routine audits to ensure regulatory alignment amidst digital growth. Generic compliance checklists rarely account for the physical-cyber overlap that defines modern ASEAN security operations.
Why efficiency alone can mislead in security operations
Here is an uncomfortable truth: the agencies with the best efficiency scores are not always the most secure. Efficiency is a moving target, and optimizing for it in isolation can quietly erode the resilience that makes security operations genuinely effective.
We have seen operations that hit elite MTTD benchmarks consistently yet failed to detect a slow-moving insider threat because their automation was tuned for speed, not depth. Short-term process optimization does not equal long-term cultural resilience. The metrics tell you how fast your machine runs. They do not tell you whether it is running in the right direction.
In the ASEAN context, this tension is sharper. Regulatory complexity, uneven digital maturity across markets, and the physical-cyber convergence unique to the region all demand contextual intelligence that no efficiency rubric fully captures. Customized sensor solutions reflect this reality: a deployment tuned for a Singapore government facility performs differently in a Philippine industrial zone, even with identical hardware.
The agencies that get this right blend metric discipline with human judgment. They treat efficiency as a floor, not a ceiling.
Pro Tip: Track ROI not just by cost savings, but by avoided losses and recovered assets over time. That is the number that tells the real story of operational value.
Accelerate your agency's efficiency with BeyondSensor
The frameworks and metrics covered here are only as powerful as the technology and expertise behind them. BeyondSensor delivers solutions for security agencies built specifically for the precision and compliance demands of Southeast Asia's government and enterprise environments.
Whether you are a system integrator deploying sensor networks across critical infrastructure or a facility owner seeking to unify physical and cyber monitoring, BeyondSensor provides the sensing technology, regional expertise, and integration support to close your efficiency gaps. From Singapore to Manila, our teams understand the local regulatory landscape and the operational realities that generic vendors overlook. The path from metrics to measurable outcomes starts with the right sensing foundation.
Frequently asked questions
What is the most reliable metric for security operational efficiency?
MTTD under 1 hour, MTTR under 4 hours, combined with automation coverage of 50 to 70% and false positive rates below 30%, are globally recognized as the most actionable efficiency metrics for SOC environments.
How can automation improve operational efficiency without causing alert fatigue?
Automation reduces repetitive analyst workload effectively, but high false positives cause burnout and over-automation risks missing nuanced threats, so routine threshold audits and human oversight layers are essential.
Why do physical and cyber security metrics differ?
Cyber metrics emphasize speed and response time, while physical sensors prioritize accuracy and low nuisance alarm rates, meaning converged operations require separate baselines and a unified escalation protocol.
What frameworks help align efficiency with compliance in Southeast Asia?
FISMA metrics via NIST CSF provide composite scoring for government agencies, while CISA CPGs establish foundational practices for critical infrastructure. Strategy mediates investments and regulatory alignment across ASEAN markets, making these frameworks essential starting points.
Recommended
Read More Articles

Top 4 Titan-SG.com Alternatives 2026
Discover 4 titan-sg.com alternatives for sensor-based security solutions and compare their features effectively.

Top advantages of sensing solutions for secure facilities
Discover the top advantages of advanced sensing solutions for security and operational efficiency in Southeast Asian industrial and smart infrastructure facilities.

Top intelligent sensing technologies to boost facility security
Discover top intelligent sensing technologies for facility security in 2026. Compare AI video analytics, environmental sensors, and access control solutions.

Understanding advanced sensing: boost security and efficiency
Learn how advanced sensing with AI, sensor fusion, and IoT boosts security accuracy and operational efficiency for industrial and government environments.
Let's Build YourSecurity Ecosystem.
Whether you're a System Integrator, Solution Provider, or an End-User looking for trusted advisory, our team is ready to help you navigate the BeyondSensor landscape.
Direct Advisory
Connect with our regional experts for tailored solutioning.