Learn how to meet physical security compliance standards with the right sensor technologies, frameworks, and implementation steps for regulated industries.

Physical security compliance: standards and sensor tech guide

Regulated industries are under more scrutiny than ever when it comes to physical security. Workplace violence now ranks as the top security concern for the second consecutive year, and organizations are spending an average of 7.6% of revenue on security programs. Yet many compliance managers still struggle to translate regulatory language into concrete sensor specifications, audit-ready documentation, and defensible system designs. This guide cuts through that complexity. You will find a clear map of the major frameworks, a breakdown of sensor technology requirements, and a step-by-step path to building a compliant, verifiable physical security program.
Table of Contents
- What is physical security compliance?
- Essential standards and regulations to know
- Sensor technologies: Required capabilities for compliance
- How to design and implement a compliant physical security system
- Ongoing verification, testing, and common pitfalls
- Take the next step: Simplify compliance with advanced solutions
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Know your standards | Identifying the correct frameworks is the first step toward effective physical security compliance. |
| Choose certified sensors | Selecting independently validated and risk-graded sensors is critical for meeting compliance requirements. |
| Follow detect-delay-respond | This framework structures compliant systems that can withstand audit and real-world incidents. |
| Benchmark and update | Routine verification and comparison to industry benchmarks help prevent compliance gaps and optimize performance. |
What is physical security compliance?
Physical security compliance means your organization's facilities, access controls, monitoring systems, and environmental safeguards meet the requirements set by applicable laws, standards, and frameworks. It is not just about installing cameras or badge readers. It is about demonstrating, through documented evidence, that your controls are appropriate for the risk level you face.
Non-compliance carries real consequences. Regulatory fines, contract disqualification, insurance penalties, and reputational damage are all on the table. For government contractors and critical infrastructure operators, a single audit failure can halt operations entirely.
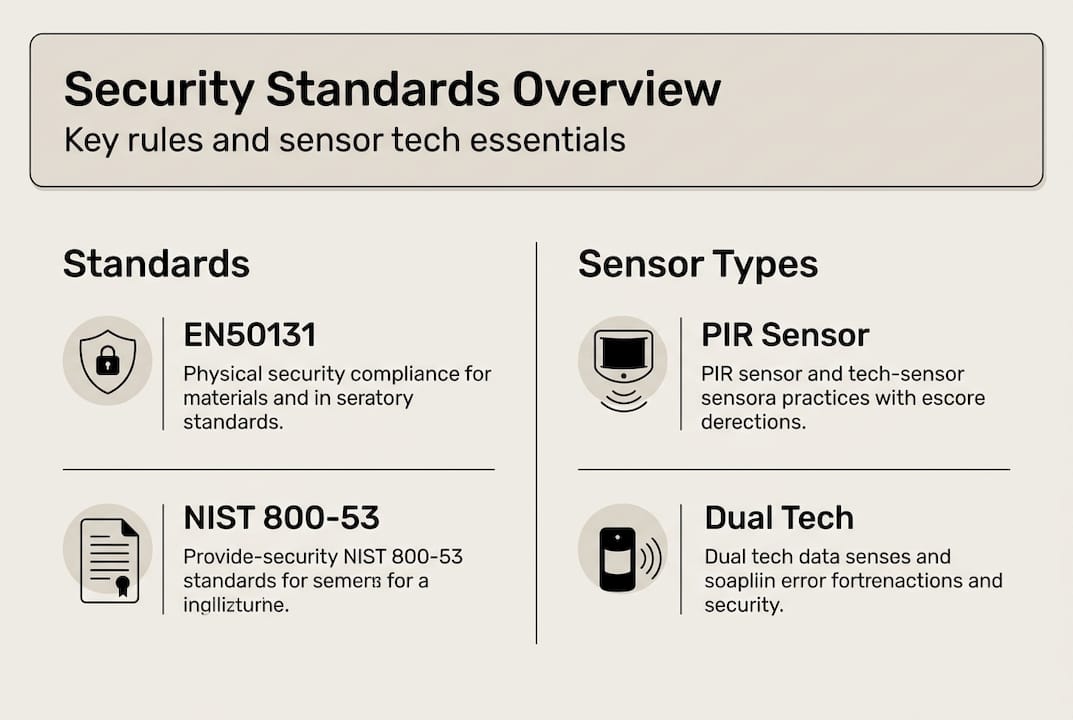
The major global standards driving physical security compliance include:
- NIST SP 800-53 Rev 5: Covers Physical and Environmental Protection controls including PE-02 Physical Access Authorizations, PE-03 Physical Access Control, PE-06 Monitoring Physical Access, and PE-14 Environmental Controls.
- ISO 27001 Annex A.7: Defines physical security controls covering perimeters, secure entry, monitoring, and equipment protection.
- DoD UFC 4-021-02: Governs electronic security system design for defense facilities.
- EN50131 and UL standards: Set graded performance requirements for intrusion detection systems.
A strong compliance program does more than satisfy auditors. It creates a baseline for continuous improvement, lets you benchmark your posture against peers, and proves program value to leadership. Explore how facility compliance requirements translate into practical system design decisions.
Essential standards and regulations to know
Every sector has its own regulatory landscape, but several frameworks appear repeatedly across industries. Understanding which ones apply to your organization is the first step toward a defensible compliance posture.
| Standard | Primary audience | Key focus areas |
|---|---|---|
| NIST SP 800-53 Rev 5 | US federal agencies, contractors | Physical and environmental controls, access management, monitoring |
| DoD UFC 4-021-02 | Defense facilities | Electronic security system design, intrusion detection, layered protection |
| ISO 27001 Annex A.7 | Global enterprises, certified organizations | Perimeter and entry controls, equipment security, monitoring |
| EN50131 | European and international markets | Graded intrusion detection, sensor performance, certification |
| UL 2050 / UL 681 | North American commercial and industrial | Alarm system installation, monitoring, and testing standards |
Several principles cut across all of these frameworks:
- Layered controls: No single sensor or barrier is sufficient. Standards require defense in depth.
- Risk-tiered requirements: Higher-risk environments face stricter sensor grades, more frequent testing, and tighter access controls.
- Documentation and auditability: Every control must be documented, tested, and traceable to a specific requirement.
- Incident response integration: Detection alone is not enough. Standards require a defined response protocol tied to each detection event.
For organizations serving government clients, understanding compliance for government users is essential. Commercial end-users can find tailored guidance through end-user security guidance resources that map standards to practical deployment scenarios.
Sensor technologies: Required capabilities for compliance
Sensors are the foundation of any compliant physical security system. Choosing the wrong type, or a product without proper certification, can invalidate your entire compliance posture. Here is a breakdown of the primary sensor types and where they fit.

| Sensor type | Standard reference | Typical application |
|---|---|---|
| Passive infrared (PIR) | EN50131-2-2 | Indoor perimeter, corridors, offices |
| Microwave | EN50131-2-3 | Large open areas, warehouses |
| Dual-technology (PIR + microwave) | EN50131-2-4 | High-security zones, false alarm reduction |
| Vibration | EN50131-2-6 | Walls, safes, vaults |
| Glass-break | EN50131-2-7 | Windows, glazed partitions |
| Active infrared (AIR) | EN50131-2-5 | Perimeter beams, entry points |
Performance grades matter enormously. EN50131 defines Grades 1 through 4, where Grade 1 covers low-risk residential environments and Grade 4 applies to high-risk facilities with professional attack scenarios. DoD UFC 4-021-02 goes further, specifying volumetric and dual-technology sensors for defense installations where detection reliability is non-negotiable.
Certification is where many programs fall short. Independent lab validation from bodies like VdS or CNPP carries far more weight than manufacturer self-declaration. Auditors know the difference, and so do insurers.
Pro Tip: Dual-technology sensors combine PIR and microwave detection, requiring both to trigger simultaneously before raising an alarm. This dramatically cuts false alarm rates and is often required for Grade 3 and Grade 4 EN50131 compliance.
For agencies and integrators deploying sensor networks at scale, sensor solutions for agencies and integration for system integrators provide deployment-ready frameworks. The advanced sensor platform at BeyondSensor supports multi-standard environments with validated, certifiable hardware.
How to design and implement a compliant physical security system
Compliance does not happen by accident. It requires a structured design process that maps every control back to a specific regulatory requirement. Here is the sequence that works.
- Conduct a scenario-based risk assessment. Identify your threat scenarios, asset criticality, and consequence levels. This determines which standards apply and at what grade level.
- Select your applicable frameworks. A US federal contractor may need NIST SP 800-53 and CMMC. A global manufacturer may need ISO 27001 and EN50131. Map your obligations before specifying any hardware.
- Choose sensors and platforms that match your grade requirements. Account for legacy systems and open architecture needs. Proprietary lock-in creates long-term compliance risk, especially when standards update.
- Implement the detect-delay-respond framework. This ASIS and CISA-endorsed model ensures your system does not just detect intrusions but delays unauthorized access long enough for a response to occur.
- Test, validate, document, and train. Every sensor zone, access point, and alarm path must be functionally tested. Documentation must be audit-ready from day one.
Safety note: High-risk and high-security environments require physical on-site inspection, not just remote configuration review. Defense manufacturing environments have demonstrated that legacy system integration and multi-factor authentication patching require hands-on validation to meet CMMC Level 2 requirements.
Pro Tip: Unified platforms that automate alarm logging, access event records, and sensor health reporting dramatically simplify audit trail generation. Manual documentation is the single biggest source of compliance gaps during audits.
The BeyondPatrol detect-delay-respond model operationalizes this framework with sensor-integrated patrol verification, giving compliance managers a defensible, documented response chain.
Ongoing verification, testing, and common pitfalls
Implementing a compliant system is only half the job. Maintaining compliance over time requires structured verification, proactive testing, and awareness of where programs typically break down.
Verification looks like this in practice: scheduled functional testing of every sensor zone, annual or biannual third-party audits, recertification when standards update, and documented corrective action for any identified gaps. It is not a one-time event.
Common pitfalls that derail compliance programs include:
- Missed standard updates: EN50131 and NIST controls are revised periodically. Programs that do not track updates fall out of compliance without realizing it.
- Unmonitored legacy systems: Older sensors and panels that are no longer actively managed create blind spots that auditors will find.
- Insufficient scenario drills: Testing that only covers normal operating conditions misses the edge cases that standards specifically require you to address.
- Self-certified sensors in regulated environments: Independent lab certification from bodies like VdS or CNPP is critical for EN50131 compliance. Self-declaration is not accepted in Grade 3 and Grade 4 environments.
- No benchmarking process: Without comparing your program against industry peers, you cannot identify where you are underinvesting or overexposed.
Pro Tip: The 2025 Security Benchmark Report shows that organizations using formal benchmarking processes demonstrate faster program maturation and stronger value justification to leadership. Build benchmarking into your annual review cycle.
The BeyondSecure benchmarking platform gives compliance managers a structured way to measure program performance, track control effectiveness, and generate the evidence needed for both internal reviews and external audits.
Take the next step: Simplify compliance with advanced solutions
Building and maintaining a compliant physical security program is demanding work. The frameworks are complex, the sensor requirements are specific, and the documentation burden is real. BeyondSensor's platforms are designed to reduce that burden without cutting corners on compliance rigor.
Whether you are managing security solutions for agencies, deploying multi-site systems through system integrator tools, or building an internal program with end-user compliance support, BeyondSensor provides validated hardware, integration-ready platforms, and regional expertise across Singapore, Malaysia, and the Philippines. Our solutions are built to align with NIST, ISO 27001, EN50131, and DoD requirements, giving you a compliance-ready foundation from day one. Reach out to our team to assess your current posture and identify the right path forward.
Frequently asked questions
Which physical security standard is mandatory for US federal agencies?
NIST SP 800-53 is the required framework for US federal agencies, covering all major physical and environmental protection controls including access authorization, monitoring, and environmental safeguards.
What are the top compliance risks with sensor-based systems?
The biggest risks are improper or self-declared certification, missed standard updates, and integration gaps when connecting legacy systems to modern platforms, particularly in defense manufacturing and critical infrastructure environments.
How can I avoid false alarms in physical security compliance?
Dual-technology sensors that require simultaneous PIR and microwave triggers, combined with proper calibration and independent lab certification, are the most effective way to reduce false alarms in compliant deployments.
What percentage of the average organization's revenue goes to security programs?
Industry benchmarks show security budgets average 7.6% of total revenue, making it one of the most significant operational expenditures for regulated organizations.
Recommended
Read More Articles

Top 4 Titan-SG.com Alternatives 2026
Discover 4 titan-sg.com alternatives for sensor-based security solutions and compare their features effectively.

Defining operational efficiency in security: insights & best practices
Learn how to define and measure operational efficiency in security with key metrics, benchmarks, and sensor strategies tailored for Southeast Asia agencies.

Top advantages of sensing solutions for secure facilities
Discover the top advantages of advanced sensing solutions for security and operational efficiency in Southeast Asian industrial and smart infrastructure facilities.

Top intelligent sensing technologies to boost facility security
Discover top intelligent sensing technologies for facility security in 2026. Compare AI video analytics, environmental sensors, and access control solutions.
Let's Build YourSecurity Ecosystem.
Whether you're a System Integrator, Solution Provider, or an End-User looking for trusted advisory, our team is ready to help you navigate the BeyondSensor landscape.
Direct Advisory
Connect with our regional experts for tailored solutioning.