Discover why security compliance is foundational to operational resilience. Learn key frameworks like IEC 62443, NIST SP 800-82, and ISO 27001 A.7, and how to integrate them across cyber and physical domains.

Security compliance: why it matters and how to master it

TL;DR:
- Compliance is essential for operational resilience, not just regulatory paperwork.
- Layering standards like IEC 62443, NIST 800-82, NIS2, and ISO 27001 creates comprehensive security coverage.
- Integrating cyber and physical controls through mapping, segmentation, and monitoring enhances real-world security.
Many security leaders treat compliance as a regulatory checkbox, something to satisfy auditors and move on. That assumption is costly. In operational environments, from industrial automation floors to critical infrastructure sites, compliance is the structural backbone of resilience. It defines how you identify vulnerabilities, control access, monitor threats, and recover from incidents. Miss a critical control, and you expose not just data but physical assets, operational continuity, and the people who depend on your systems. This article breaks down the standards that matter, how they work together, and how to build a compliance strategy that actually strengthens your security posture.
Table of Contents
- What makes compliance essential in security?
- Core compliance frameworks for security: OT and physical domains
- Strategies for integrating compliance across cyber and physical security
- Practical benefits of compliance for critical infrastructure and operations
- A security expert's perspective: What most compliance guides miss
- Take the next step: Solutions for seamless security compliance
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Compliance builds resilience | By meeting standards, you protect operations from both cyber and physical threats. |
| Stack standards for strength | Combining frameworks like IEC 62443, NIST SP 800-82, and ISO 27001 creates layered security. |
| Integration unlocks efficiency | Bridging compliance across cyber and physical domains reduces risk and boosts operational continuity. |
| Advanced sensing powers compliance | Smart sensors and monitoring tools automate controls, reporting, and asset protection. |
What makes compliance essential in security?
Compliance in security is not about paperwork. It is about systematically reducing the risk that operational environments face every day. For security managers working across industrial automation and physical security, this means addressing threats at both the cyber and physical layers simultaneously.
The challenge is that most organizations treat these layers separately. IT teams manage firewalls and patch cycles. Facilities teams manage badge readers and perimeter fencing. Neither group talks to the other consistently. The result is a fragmented posture where gaps at the intersection of cyber and physical controls become the most exploitable attack surface.
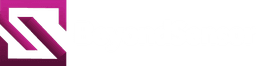
Strong security compliance frameworks address this by requiring organizations to document, test, and continuously monitor controls across both domains. Key standards for OT security compliance include IEC 62443 for lifecycle security, NIST SP 800-82 for ICS technical guidance, and NIS2 for governance and reporting. On the physical side, ISO 27001 Annex A.7 requires perimeters, monitoring, and access controls to protect assets alongside digital security.
Compliance frameworks also serve security agencies and operators who need structured evidence of due diligence for regulatory bodies, insurers, and stakeholders.
"Compliance is not a destination. It is an ongoing operational discipline that keeps your defenses aligned with evolving threats."
Here is what a well-executed compliance program delivers:
- Reduced risk across cyber and physical attack surfaces
- Improved resilience through tested, documented controls
- Easier audits with traceable evidence and structured reporting
- Operational continuity by preventing incidents before they escalate
- Stakeholder confidence through demonstrated security maturity
Pro Tip: Avoid siloed compliance checklists. Integrated controls that address both cyber and physical domains simultaneously are far more effective than separate audit tracks that never intersect.
Core compliance frameworks for security: OT and physical domains
With the value of compliance clear, let's break down the main standards that underpin operational and physical security.
Four frameworks dominate the landscape for industrial and physical security environments. Each has a distinct scope, but they are designed to complement each other rather than compete.
| Framework | Primary focus | Key mechanism | Best for |
|---|---|---|---|
| IEC 62443 | OT/ICS lifecycle security | Zones, conduits, security levels | Industrial automation, manufacturing |
| NIST SP 800-82 | ICS technical hardening | Configuration guidance, risk assessment | Critical infrastructure operators |
| NIS2 | Governance and regulatory reporting | Incident reporting, supply chain risk | EU-regulated sectors |
| ISO 27001 Annex A.7 | Physical security controls | Perimeters, access, environmental controls | Facilities, data centers, mixed environments |
IEC 62443 covers zones and conduits with defined security levels, while NIST SP 800-82 provides hardening without breaking operations. Stack them for resilience. This is not theoretical advice. Organizations that layer these frameworks close the gaps that single-framework approaches leave open.
A useful physical security guide confirms that physical and cyber controls must be mapped together to prevent adversaries from bypassing digital defenses through physical access.
For system integrators deploying across multiple client environments, understanding which frameworks apply to each sector is critical. A water treatment facility has different NIS2 obligations than a logistics hub. Facility owners benefit most from ISO 27001 Annex A.7 as a starting point, then layering IEC 62443 where operational technology is present.
Key priorities across these frameworks include:
- Lifecycle security from design through decommissioning (IEC 62443)
- Operational safety without disrupting production processes (NIST SP 800-82)
- Asset protection through physical perimeter and access controls (ISO 27001 A.7)
- Regulatory reporting with documented incident response timelines (NIS2)
Research consistently shows that a significant share of breaches involve gaps in compliance controls, particularly at the boundary between IT and OT networks. Closing those gaps requires more than a single standard. It requires a layered approach.
Strategies for integrating compliance across cyber and physical security
Understanding frameworks is essential, but integration across domains is what unlocks true operational security.
The most common mistake security managers make is treating physical and cyber compliance as parallel tracks that never merge. This creates blind spots. A threat actor who gains physical access to a network cabinet bypasses every firewall rule you have. Integration eliminates that blind spot.
Here is a practical stepwise process for integrating compliance across both domains:
- Map your assets across both cyber and physical environments. Every sensor, controller, access point, and network segment needs to be documented.
- Identify applicable frameworks for each asset class. OT systems need IEC 62443 and NIST SP 800-82. Physical perimeters need ISO 27001 A.7. Regulated sectors add NIS2.
- Define zones and conduits using IEC 62443 principles. Segment your network to limit lateral movement and map physical access zones to match logical boundaries.
- Apply technical hardening using NIST SP 800-82 guidance. Prioritize availability and safety over aggressive patching that could disrupt operations.
- Establish monitoring across both domains. Physical intrusion detection and cyber anomaly detection should feed into a unified operations center.
- Document and test all controls. Compliance evidence must be traceable, current, and audit-ready.
"Stack standards for resilience: NIS2 outcomes combined with IEC lifecycle controls and NIST operational guidance create a defense posture that no single framework achieves alone."
For end users operating legacy OT systems, digital twins and micro-segmentation are powerful tools. Digital twins allow you to model and test compliance changes without touching live production systems. Micro-segmentation limits the blast radius if a legacy device is compromised.
Refer to this integrated security guide for additional context on bridging physical and cyber controls at the operational level.
Pro Tip: For legacy OT environments, use digital twins to simulate compliance changes before deployment. Micro-segmentation around aging devices limits exposure without requiring costly hardware replacement.
BeyondSecure is designed with this integration challenge in mind, offering sensing and monitoring capabilities that span both physical and cyber security requirements.
Practical benefits of compliance for critical infrastructure and operations
Now, let's explore the practical and operational benefits security compliance delivers in real-world environments.
Compliance is often framed as a cost center. The reality is the opposite. Organizations that build strong compliance programs see measurable operational improvements, not just audit pass rates.
Controls including A7.1 perimeters, A7.4 monitoring, and A7.5 environmental threat protections integrate physical and digital defenses into a coherent operational framework. When these controls are active and monitored, incidents are detected earlier, response times drop, and recovery is faster.
| Compliance outcome | Operational benefit |
|---|---|
| Documented asset inventory | Faster incident response and root cause analysis |
| Continuous monitoring (A7.4) | Earlier threat detection, reduced dwell time |
| Environmental controls (A7.5) | Protection against power, temperature, and physical threats |
| Structured incident reporting | Streamlined regulatory submissions, reduced penalty risk |
| Access control enforcement | Reduced insider threat and unauthorized access incidents |
Advanced sensing technologies strengthen compliance by providing the real-time data that monitoring controls require. Sensors that track environmental conditions, motion, access events, and network anomalies feed directly into compliance evidence. This is where security tools built for operational environments deliver a genuine advantage over generic IT solutions.
Refer to this compliance monitoring guide for structured approaches to continuous monitoring in security operations.
Key operational benefits of a mature compliance program include:
- Risk reduction through proactive control testing and gap remediation
- Efficiency gains from automated monitoring and reporting workflows
- Outage prevention by identifying vulnerabilities before adversaries exploit them
- Audit readiness with continuously updated, traceable control evidence
Pro Tip: Deploy monitoring controls aligned to ISO 27001 A7.4 and environmental controls aligned to A7.5 across both your cyber and physical assets. This dual coverage satisfies multiple framework requirements simultaneously and reduces the total compliance workload.
A security expert's perspective: What most compliance guides miss
With operational benefits established, it is time to address what mainstream compliance advice consistently overlooks.
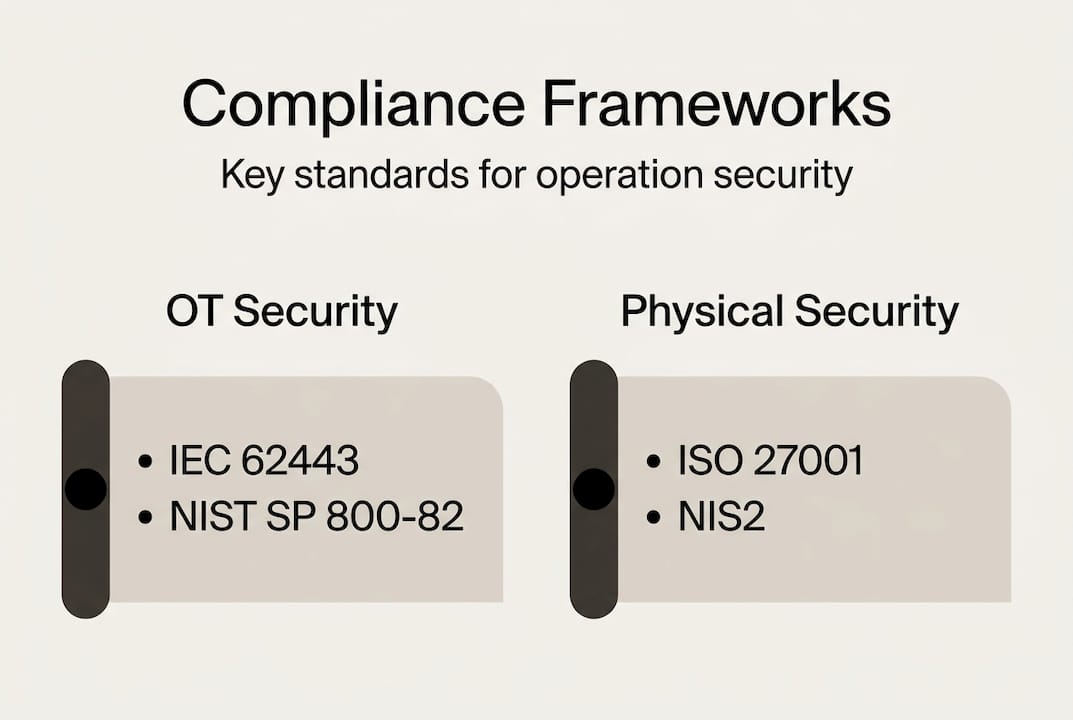
Most compliance guides are written for IT environments. They assume you can patch systems on a schedule, reboot devices without consequence, and segment networks without affecting production. In OT and physical security environments, none of those assumptions hold.
The real gap is not knowledge of the frameworks. It is the failure to adapt them to operational realities. Stacking standards, prioritizing safety and availability over IT patching, and using digital twins with micro-segmentation are expert-level approaches that most guides skip entirely.
We see this repeatedly: organizations pass audits by checking boxes but remain operationally exposed because their compliance strategy was never designed for their actual environment. Compliance that does not account for legacy OT constraints, physical perimeter realities, and operational uptime requirements is compliance theater, not operational resilience.
For government users and critical infrastructure operators, the stakes are too high for that approach. Build compliance strategies that adapt to your operational context, not the other way around. Resilience is the goal. Audit passage is the byproduct.
Take the next step: Solutions for seamless security compliance
Seeing why compliance matters is the first step. Acting on it with the right tools is what separates secure operations from vulnerable ones.
BeyondSensor delivers advanced sensing and AI-based monitoring solutions purpose-built for security managers who need compliance without operational disruption. Whether you are a security agency managing critical infrastructure or one of our system integrators deploying across industrial environments, our platform supports IEC 62443, NIST SP 800-82, NIS2, and ISO 27001 A.7 requirements. Explore our advanced AI compliance tools to see how intelligent sensing automates evidence collection, continuous monitoring, and audit-ready reporting across both cyber and physical domains.
Frequently asked questions
Why is compliance critical for security operations?
Compliance ensures risk management at both cyber and physical levels, providing the structured controls and documented evidence needed to maintain operational continuity and defend against evolving threats.
Which security compliance frameworks are most relevant for industrial environments?
IEC 62443, NIST SP 800-82, and NIS2 are the primary OT security standards, and ISO 27001 Annex A.7 adds the physical security layer needed for complete coverage in industrial environments.
How can compliance be integrated across cyber and physical domains?
Stack multiple standards to cover lifecycle, technical hardening, governance, and physical controls simultaneously, then use advanced sensing technologies to automate monitoring across both domains.
What are the operational benefits of meeting security compliance requirements?
Compliance delivers risk reduction, resilience, and audit readiness alongside practical gains like faster incident response, reduced downtime, and streamlined regulatory reporting.
Recommended
- BeyondSecure | Innovation | BeyondSensor
- BeyondSensor | Advanced AI Solutions
- BeyondPatrol: Redefining Security with VLM-Powered Virtual Guard Tours | News | BeyondSensor
- BeyondSensor | Advanced AI Solutions
- What is security compliance? Key frameworks and real-world steps
- GDPR Compliance: Why It Matters in UK Security | Security Jobs Board
Read More Articles

Top 4 Titan-SG.com Alternatives 2026
Discover 4 titan-sg.com alternatives for sensor-based security solutions and compare their features effectively.

Defining operational efficiency in security: insights & best practices
Learn how to define and measure operational efficiency in security with key metrics, benchmarks, and sensor strategies tailored for Southeast Asia agencies.

Top advantages of sensing solutions for secure facilities
Discover the top advantages of advanced sensing solutions for security and operational efficiency in Southeast Asian industrial and smart infrastructure facilities.

Top intelligent sensing technologies to boost facility security
Discover top intelligent sensing technologies for facility security in 2026. Compare AI video analytics, environmental sensors, and access control solutions.
Let's Build YourSecurity Ecosystem.
Whether you're a System Integrator, Solution Provider, or an End-User looking for trusted advisory, our team is ready to help you navigate the BeyondSensor landscape.
Direct Advisory
Connect with our regional experts for tailored solutioning.