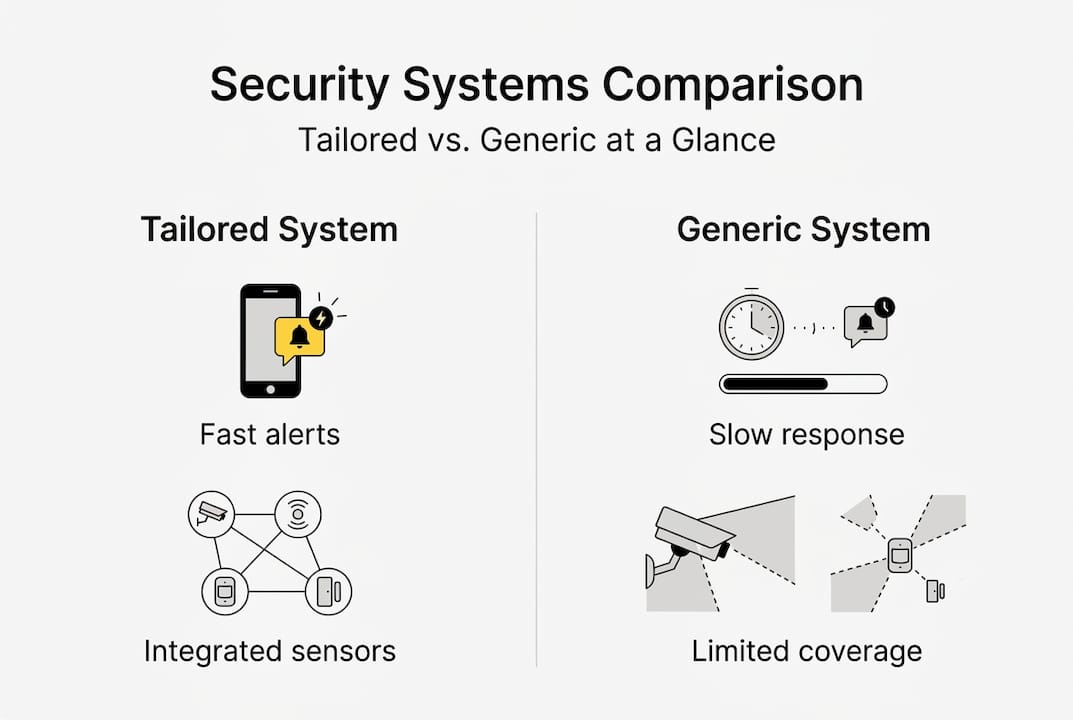
Discover why tailored sensor-based security solutions cut response times by up to 95% and outperform generic systems for Southeast Asia facility managers.

Why tailored security solutions outperform generic systems

Most security managers in Southeast Asia have inherited a generic system at some point. Standard motion detectors, off-the-shelf cameras, and a one-size-fits-all control panel. It feels adequate until a false alarm floods the monitoring center at 2 a.m., or a perimeter breach goes undetected because the sensor wasn't rated for tropical humidity. Tailored solutions outperform generic ones in Southeast Asia by adapting to urban density, tropical resilience, and labor shortages through automation. This guide breaks down exactly how that works and what it means for your facility.
Table of Contents
- Why tailored security solutions matter in Southeast Asia
- Exploring sensor technologies for multi-layered protection
- Boosting operational efficiency and compliance with tailor-fit systems
- Integrating human expertise with sensor automation: Best practices
- Transform security with tailored solutions from BeyondSensor
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Customized solutions are crucial | Tailored systems address Southeast Asia’s unique security and compliance demands far better than generic setups. |
| Multi-layered sensor integration | Combining fiber optic, LiDAR, PIR, and other sensors creates comprehensive perimeter and interior protection. |
| Significant efficiency gains | Custom systems reduce response times by up to 95% and help facilities meet regulatory and sustainability goals. |
| Human-plus-automation best practices | Integrating human expertise with sensor networks delivers robust verification, context, and rapid escalation. |
Why tailored security solutions matter in Southeast Asia
Southeast Asia is not a single security environment. A logistics hub in Manila, a data center in Singapore, and a manufacturing plant in Kuala Lumpur each face radically different threat profiles. Urban density compresses response windows. Tropical heat and monsoon flooding degrade sensors not built for the climate. And tightening labor markets make round-the-clock human patrols increasingly expensive and unreliable.
These are not edge cases. They are the baseline conditions your security system must handle every single day. Generic systems are engineered for average conditions in temperate climates with stable labor pools. They were never designed for your operating environment.
Key regional drivers that demand customization include:
- Tropical climate stress: High humidity, heat, and flooding cycles accelerate hardware failure in standard sensors.
- Urban density: Overlapping signal zones and high foot traffic generate excessive false alarms in generic setups.
- Labor shortages: Automation must compensate where human guard coverage is thin or inconsistent.
- Regulatory pressure: Governments across the region are raising compliance requirements for critical infrastructure and commercial facilities.
- Multi-site complexity: Facility owners managing multiple properties need centralized, scalable architectures that generic vendors rarely offer.
Effective urban security planning accounts for all of these variables before a single sensor is installed. And when you work with government user solutions that understand regional compliance frameworks, the gap between a generic rollout and a tailored deployment becomes impossible to ignore.
"A security system that wasn't designed for your environment isn't a security system. It's a liability with a power cable."
Exploring sensor technologies for multi-layered protection
Tailored deployments don't rely on a single sensor type. They use a defense-in-depth approach, stacking perimeter, vicinity, and indoor detection layers so that a threat must defeat multiple independent systems before it reaches a critical asset.
Here's how the sensor layers map to real-world deployment zones:
| Layer | Sensor type | Primary function |
|---|---|---|
| Perimeter | Fiber optic cable | Detects vibration and intrusion along fences or walls |
| Perimeter | LiDAR (long range) | Creates a 3D detection field across open ground |
| Vicinity | REDSCAN LiDAR | Monitors building approaches and blind spots |
| Indoor | PIR sensors | Detects body heat movement in corridors and rooms |
| Indoor | Dual tech sensors | Combines PIR and microwave to cut false alarms |
| All layers | CCTV integration | Provides visual verification of sensor-triggered alerts |
| All layers | Access control | Locks down zones automatically on confirmed breach |
Fiber optic sensors are particularly valuable in Southeast Asia because they are immune to electromagnetic interference and perform reliably in wet conditions. LiDAR adds precision that camera-based systems simply cannot match in low-light or smoke-filled environments.

The real power of multi-layered security comes from integration. When a perimeter LiDAR detects movement, it triggers the nearest CCTV camera to pan and zoom, sends an alert to the control room, and simultaneously locks the relevant access points. That chain of events happens in seconds, not minutes.
For end user deployments, the combination of sensor integration with access control and video analytics creates a system that actively responds rather than passively records.
Pro Tip: When specifying sensors for outdoor perimeter use in tropical climates, always verify the IP rating. IP66 is the minimum for monsoon-prone locations. IP67 or IP68 is strongly recommended for flood-risk zones.
Boosting operational efficiency and compliance with tailor-fit systems
Security is not just about stopping threats. For facility owners and security managers, it is also about operational continuity, audit readiness, and meeting the standards that regulators and insurers increasingly demand.
Custom sensor systems deliver measurable gains across all three areas. The numbers are striking: response times drop 90 to 95% in documented deployments when tailored sensor networks replace generic setups. That is not a marginal improvement. It is the difference between containing an incident and managing a crisis.
Tailored vs. generic systems: efficiency comparison
| Metric | Generic system | Tailored system |
|---|---|---|
| Detection-to-alert time | 3 to 8 minutes | Under 30 seconds |
| False alarm rate | High (15 to 30%) | Low (under 5%) |
| Compliance documentation | Manual, inconsistent | Automated, audit-ready |
| Energy consumption | Fixed, unoptimized | Adaptive, ESG-aligned |
| Scalability | Limited | Modular and expandable |
Tailored systems also support alignment with ISO 22301 for business continuity management and NFPA 1600 for disaster and emergency management. Energy-efficient sensors contribute directly to ESG reporting, which is becoming a procurement requirement for large commercial and government contracts across the region.
Here is a practical sequence for moving from assessment to operational gains:
- Site risk assessment: Map threat vectors, environmental conditions, and compliance requirements specific to your facility.
- Sensor selection: Match sensor types to each zone based on the risk profile and environmental constraints.
- Integration design: Define how sensors, CCTV, access control, and monitoring platforms communicate.
- Pilot deployment: Test the system in a controlled zone before full rollout to validate performance.
- Staff training: Ensure your team understands alert protocols, escalation paths, and system maintenance.
- Compliance audit: Document system capabilities against ISO 22301, NFPA 1600, or applicable local standards.
Working with facility owner solutions that understand this sequence prevents the costly rework that comes from skipping steps. System integrator expertise is especially valuable at the integration design stage, where poor decisions create bottlenecks that no amount of hardware can fix later. The right sensor system efficiency approach treats security and operations as a single discipline, not two separate budgets.
Integrating human expertise with sensor automation: Best practices
Automation handles volume. Humans handle judgment. The most effective security operations in Southeast Asia understand this distinction and build their protocols around it.
Sensors generate alerts at a scale no human team can match. A fiber optic perimeter system monitoring a 2-kilometer fence line produces data continuously. Expecting guards to manually interpret every signal is unrealistic and counterproductive. Automation filters, prioritizes, and routes alerts so that human attention goes where it matters most.
But automation has limits. A sensor cannot distinguish between a contractor working late and an unauthorized intruder. It cannot assess whether a triggered alert warrants a police call or a routine check. Integrating human guards with sensors for verification is what closes that gap.
Best practices for blending human and automated security:
- Define clear escalation protocols: Every alert category should have a documented response path, from automated lockdown to human verification to external escalation.
- Give guards real-time sensor access: Guards should see live sensor data and camera feeds on mobile devices, not just receive radio calls after the fact.
- Train for automation failures: Systems go offline. Guards must know how to maintain security posture manually when sensors or software fail.
- Review alert logs regularly: Weekly reviews of false alarm patterns help you tune sensor sensitivity and reduce guard fatigue from unnecessary responses.
- Avoid over-automation: Removing humans entirely from the verification loop creates blind spots that sophisticated intruders can exploit.
For security agency tips on structuring guard-sensor workflows, the key insight is that automation should amplify human capability, not replace human judgment. The virtual guard best practices model demonstrates how remote monitoring combined with on-site sensor networks can extend coverage without proportionally increasing headcount.
Pro Tip: Run quarterly tabletop exercises where your security team responds to simulated sensor alerts without automation support. This builds the muscle memory needed when systems fail and reveals gaps in your escalation protocols before a real incident does.
Transform security with tailored solutions from BeyondSensor
The gap between a generic security setup and a tailored sensor deployment is not just technical. It shows up in your incident reports, your compliance audits, and your operational costs every month.
BeyondSensor designs and deploys custom sensor-based security solutions for facilities across Singapore, Malaysia, the Philippines, and the broader Southeast Asian region. Whether you manage a single critical site or a portfolio of commercial properties, our team works with security agency solutions and system integrator offerings to build architectures that match your threat profile, your compliance requirements, and your operational goals. Discover BeyondSensor and connect with our regional experts to start building a security system that was actually designed for your environment.
Frequently asked questions
How do tailored security solutions respond faster than generic systems?
Tailored sensor networks cut response times 90 to 95% by combining perimeter, vicinity, and indoor sensors with automated alert routing and real-time monitoring, eliminating the manual handoffs that slow generic systems down.
Which sensor types are most effective for perimeter security?
Fiber optic and LiDAR sensors lead perimeter detection for their range and environmental resilience, while PIR and dual tech sensors are better suited to indoor zones where precision and false alarm reduction matter most.
What standards do tailored security systems help facilities meet?
Custom solutions are built to align with ISO 22301 and NFPA 1600, and energy-efficient sensor choices directly support ESG reporting requirements that are increasingly tied to government and commercial contracts in Southeast Asia.
How do human guards and sensors work together?
Automation handles continuous monitoring and alert prioritization, while human guards provide the contextual judgment needed for verification and escalation decisions that sensors alone cannot make reliably.
Recommended
Read More Articles

Top 4 Titan-SG.com Alternatives 2026
Discover 4 titan-sg.com alternatives for sensor-based security solutions and compare their features effectively.

Defining operational efficiency in security: insights & best practices
Learn how to define and measure operational efficiency in security with key metrics, benchmarks, and sensor strategies tailored for Southeast Asia agencies.

Top advantages of sensing solutions for secure facilities
Discover the top advantages of advanced sensing solutions for security and operational efficiency in Southeast Asian industrial and smart infrastructure facilities.

Top intelligent sensing technologies to boost facility security
Discover top intelligent sensing technologies for facility security in 2026. Compare AI video analytics, environmental sensors, and access control solutions.
Let's Build YourSecurity Ecosystem.
Whether you're a System Integrator, Solution Provider, or an End-User looking for trusted advisory, our team is ready to help you navigate the BeyondSensor landscape.
Direct Advisory
Connect with our regional experts for tailored solutioning.